KessV2 ECU remapping tool - Our rating 10/10
The KessV2 allows chip tuners to easily read and write chip tuning files to the engine control unit ( ECU) of different vehicles. The Kess V2 is an OBD tuning tool which connects to the vehicle through the OBD port. The KessV2 can tune the following vehicles within minutes through the OBD port of the vehicle:
- Cars
- Bikes
- Boats
- Agricultural vehicles
- Trucks
- DSG gearboxes
Why we like it - The Kess can tune over 6000 vehicles and probably has the largest selection of tuneable vehicles through the OBD port. Due to the price, the simplicity of the tool, the reliability during reading and writing and the number of vehicles that the KessV2 can tune it is our preferred tool for first-time users. : This attempts to "break out" of the
Price - The Kess starts from 1 500 Euro and go up to 4 500 Euro. The price of chip tuning tools depends on the protocols and if it is a master or slave tool. Both pricing aspects are discussed on the page below : This is the heart of the attack
Supported vehicles - Click here to download the full vehicle list of the KessV2 What is this string
Services that can be offered with the KessV2 - With the Kess V2 chip tuning tool you can read and write tuning files through the OBD port of the vehicle. Once you are able to read and write tuning files you can offer services such as performance tuning, custom tuning, DSG tuning, and DTC deletes. For more information on the service you can offer please visit our service page.
Chip Tuning File - Once you have a Kess V2 you will need a chip tuning files to write to the car. Tuned2Race can supply you with a wide range of chip tuning files for all the services you plan to offer. For more information on chip tuning files, please visit our chip tuning file page
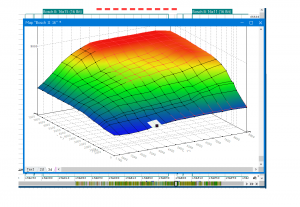
KessV2 Overview
The KessV2 is an OBD chip tuning tool that can read and write chip tuning files for over 6000 vehicles through the OBD port
{keyword}') Union All Select Null,null,null,null,null,null,null,null-- Mxyc May 2026
: This attempts to "break out" of the developer’s intended code by closing a data field and a function.
It looks like you've included a in your request. In the world of cybersecurity, that specific snippet is a classic example of an "Union-based" attack.
: This is the heart of the attack. It tells the database to combine the results of the original (legitimate) search with a new set of data the attacker wants to see.
Here is a look into what that string is designed to do and why it’s a fundamental concept in web security. What is this string?
Modern web development has largely moved past this threat using a technique called (or Parameterized Queries). Instead of letting user input mix directly with the code, the database is told: "Treat this input strictly as text, no matter what symbols are inside it."
If a website is vulnerable to this, an attacker doesn't just stop at NULL . They eventually replace those NULL s with commands to extract sensitive info—like your —and display them right on the screen where the "Keyword" results should have been. How Developers Stop This
Our promise to you
Custom ECU Tuning solutions
We will develop and adjust our software until you are 100% satisfied with our service.
Reliable service
We strive to provide motoring enthusiasts with performance solutions that don't exceed the manufactures safety limits.
Money back guarantee
If our service doesn't live up to your expectations we will happily refund you.
: This attempts to "break out" of the developer’s intended code by closing a data field and a function.
It looks like you've included a in your request. In the world of cybersecurity, that specific snippet is a classic example of an "Union-based" attack.
: This is the heart of the attack. It tells the database to combine the results of the original (legitimate) search with a new set of data the attacker wants to see.
Here is a look into what that string is designed to do and why it’s a fundamental concept in web security. What is this string?
Modern web development has largely moved past this threat using a technique called (or Parameterized Queries). Instead of letting user input mix directly with the code, the database is told: "Treat this input strictly as text, no matter what symbols are inside it."
If a website is vulnerable to this, an attacker doesn't just stop at NULL . They eventually replace those NULL s with commands to extract sensitive info—like your —and display them right on the screen where the "Keyword" results should have been. How Developers Stop This