
Choose any of the searching criteria to restore lost data. Here we are going to select 'Photo Search' mode for demonstration purpose.
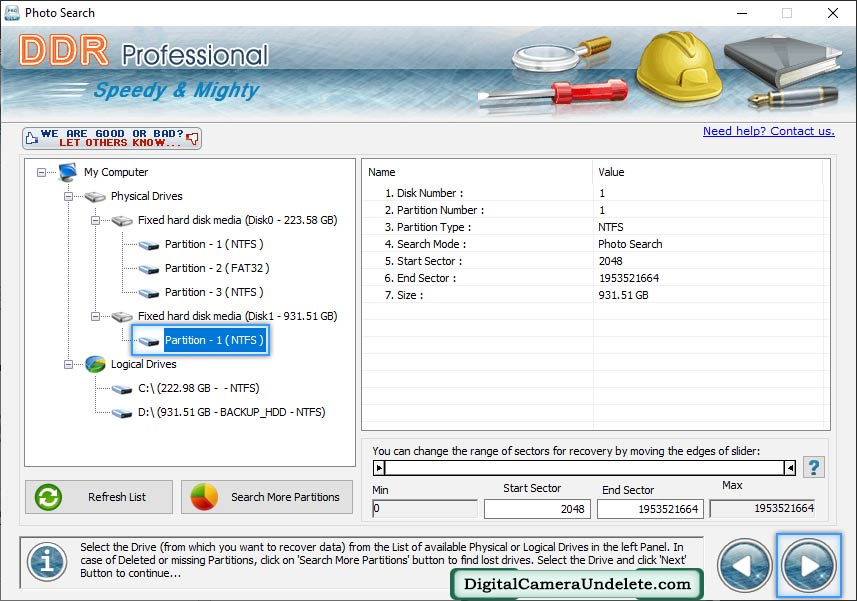
Select disk partition or drive from which you want to recover data. In case of deleted or missing partitions, click on 'Search More Partitions' button.
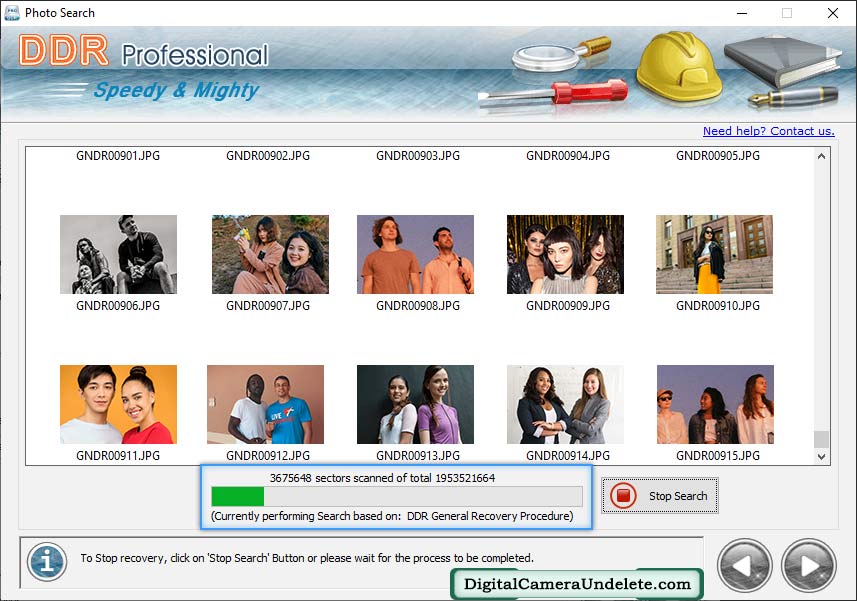
Currently performing scanning process, You can stop searching process by clicking on "Stop" button.
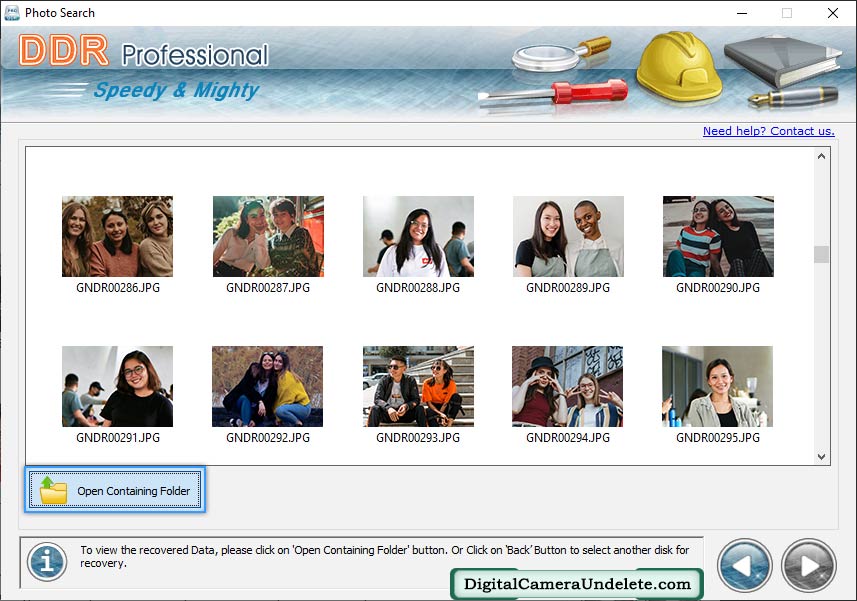
Data has been recovered successfully. To view your recovered data, click on 'Open Containing Folder' button.
As they celebrated their victory, Dr. Kim turned to Alex and said, "You know, sometimes the most complex problems require a deep understanding of geometry and creative thinking." Alex nodded in agreement, and they both looked forward to their next adventure in the world of geometric innovation.
After some deliberation, Alex suggested that they try to understand the underlying geometry of the Glovius software. By analyzing the code and the geometric algorithms used, they might be able to create a new, legitimate license key. As they celebrated their victory, Dr
The challenge was on! Dr. Kim and Alex worked tirelessly, pouring over lines of code and geometric equations. As they worked, the laboratory around them transformed into a geometric wonderland, with shapes and patterns emerging from the walls and ceiling. By analyzing the code and the geometric algorithms
As they deciphered the message, they discovered that the "790_Crack" user had created a patch that could bypass the license key verification process. However, Dr. Kim was hesitant to use the patch, as she was concerned about its safety and legitimacy. Kim and Alex worked tirelessly, pouring over lines
And so, the story of the Geometric Glove and the Glovius software came full circle, as Dr. Kim and Alex continued to push the boundaries of what was possible with geometry and technology.
As she was testing the glove's prototype, version 6.0.0, she encountered an unexpected challenge. The glove's software, which she had dubbed "Glovius," required a special license key to function properly. However, the key she had generated earlier seemed to have expired, and she couldn't find a way to reactivate it.